Attackers don't break in. They log in.
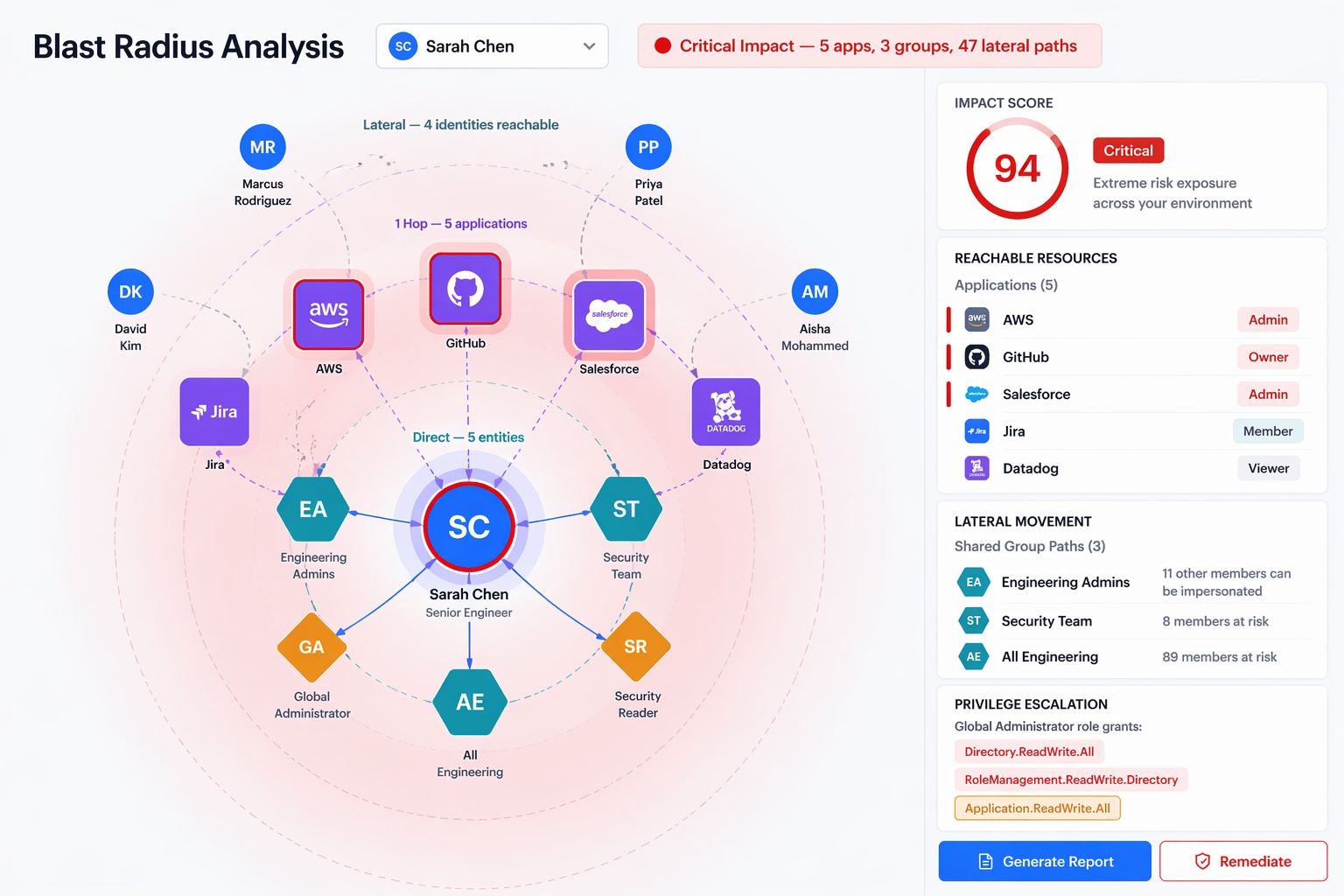
Find the stale admin, the over-scoped principal, the MFA gap, the legacy protocol nobody disabled. Fix them before they become the breach.

Find the stale admin, the over-scoped principal, the MFA gap, the legacy protocol nobody disabled. Fix them before they become the breach.

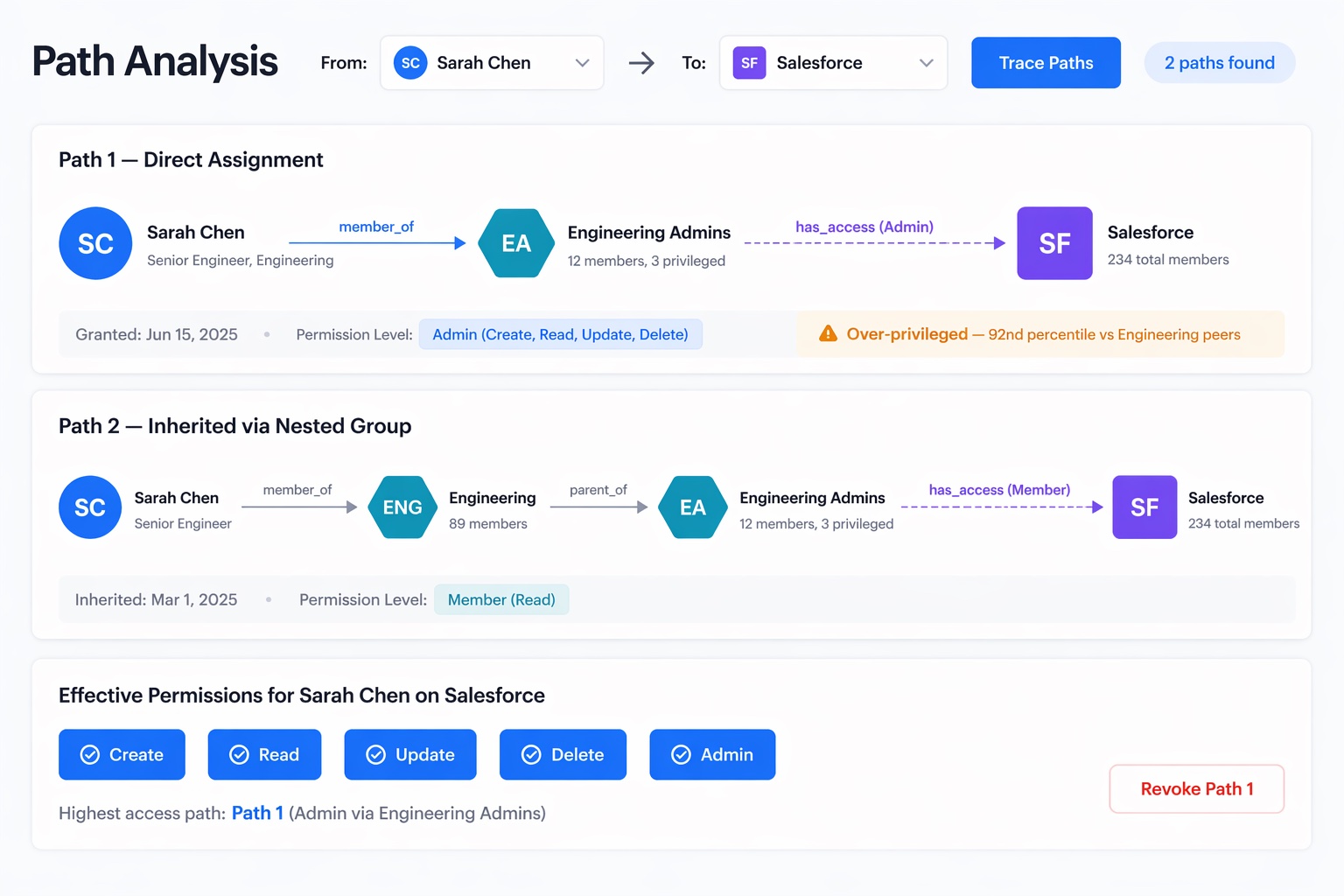
Nested group membership. Inherited role. OAuth scope creep. Shadow admin permissions not in any admin group. Your IdP console doesn't tell you.
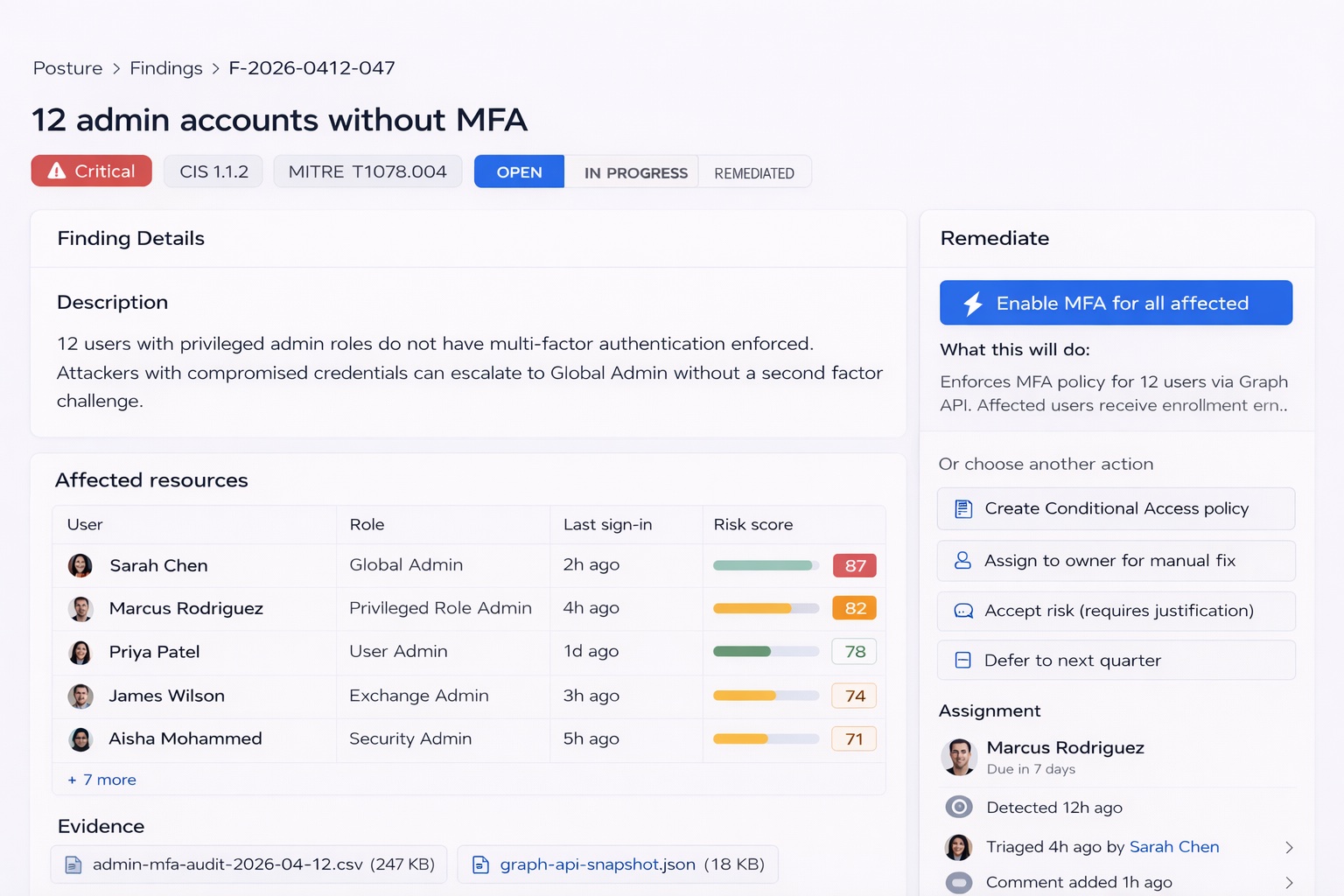
MFA coverage looks fine until you check the 12 admin accounts with no second factor, or the service principals with permanent tokens that never expire.
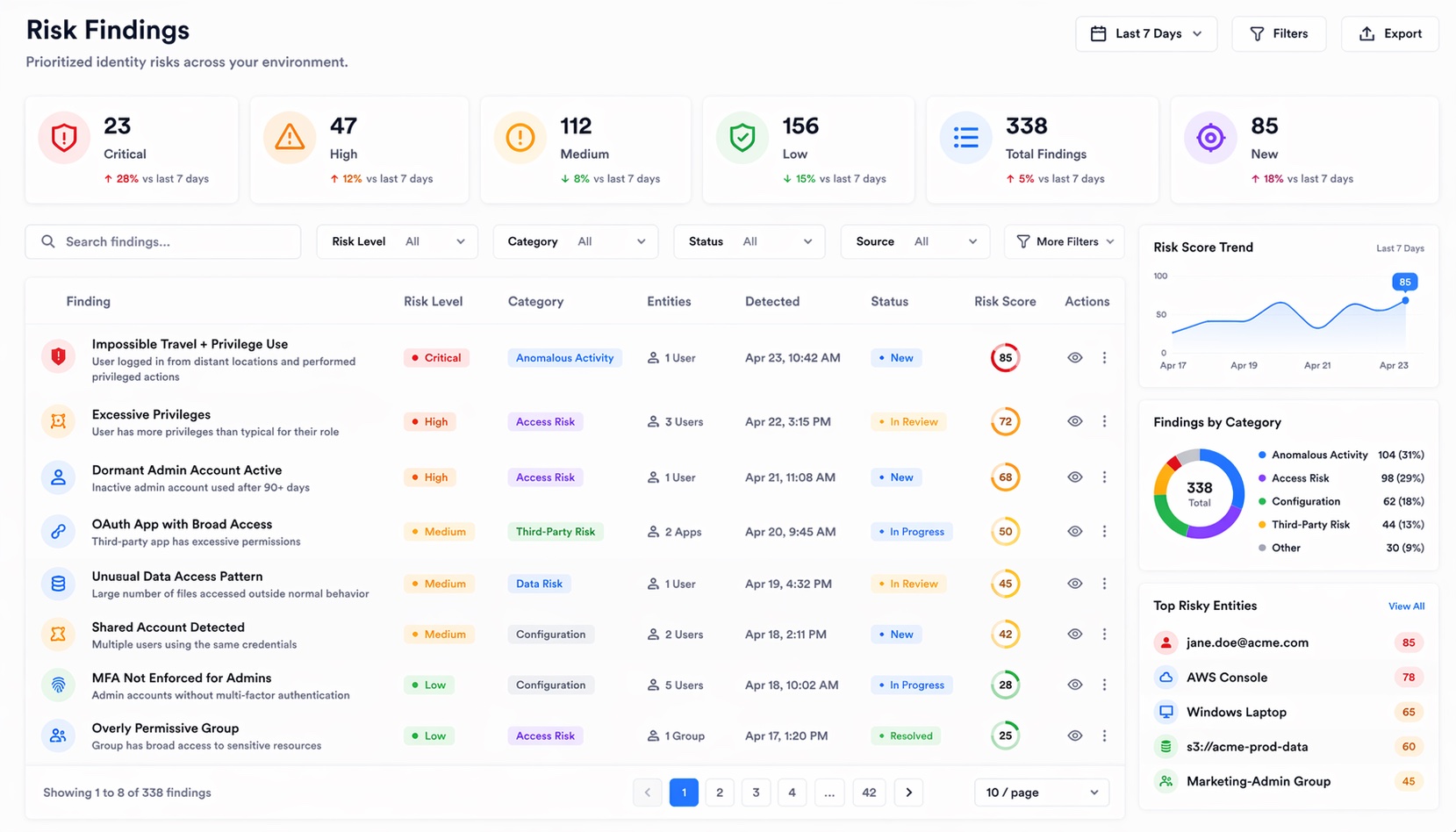
Your posture tool generates 1,400 findings. Nobody knows which ones to fix first, and there's no workflow to close them. The list just grows.


Silverfort, Zluri, Lumos, Microsoft, Okta — all ship posture and governance as separate products. We built them on one data layer.
Posture finds 47 users with admin roles but no admin privilege usage in 90 days.
Finding automatically spawns a Govern access review campaign. Reviewers see risk context inline.
Reviewers revoke. Posture score improves automatically. Loop closed without leaving the platform.
Ranks findings by exploitability plus blast radius, not just severity. Configuration drift predictor learns normal change patterns and flags anomalies. Posture forecasting predicts your score trajectory. Auto-remediation closes low-risk findings without human approval.
Find every privileged account without MFA. Enforce it in one action.
12 admin accounts dormant 6+ months. Each one a free entry point for an attacker.
Over-permissioned SPs with no owner, no expiry. Fastest-growing attack surface.
NTLMv1, weak LDAP, legacy auth bypasses your MFA. Find them. Block them.
Visualize which users, apps, and actions aren't covered by any CA policy.
One score. Trend line. Industry comparison. Every month, zero spreadsheets.
You probably don't know. Most teams find 30-50 critical findings in their first scan. See yours.